Welcome to our in-depth guide on how to effectively use the FuseAIOpenChat-3.5-7B-Mixtral-v2.0 model! This blog will walk you through the essential steps for utilizing this powerful AI model, including downloading required files, quantization details, and...
Unlocking the Power of CAMEL-13B: A Comprehensive Guide
In the ever-evolving world of artificial intelligence, large language models (LLMs) hold the key to transformative changes in how we communicate and interact with machines. Today, we delve into the specifics of the CAMEL-13B-Combined-Data, a model that stands out...
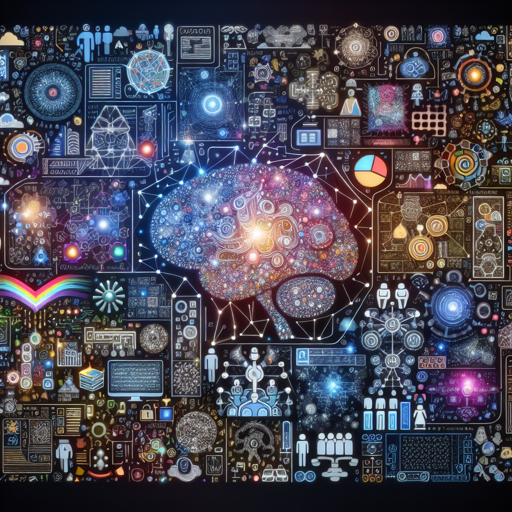
How to Request Access to SkufidonKvashenaya Model
Access to cutting-edge AI models can sometimes feel like trying to enter an exclusive club. And in the case of the SkufidonKvashenaya model, the bouncers are strict; unauthorized users are not admitted. No need to fret though! This guide will help you navigate the...
How to Train the ALBERT Model on SQuAD v2
In this blog post, we will walk you through the process of training the ALBERT base v2 model on the SQuAD v2 dataset. Whether you are a beginner or an experienced practitioner in the realm of Natural Language Processing, this guide aims to be user-friendly and...
Understanding Concept Sliders for AI Image Generation
Welcome to the world of AI image generation! Today, we’re diving into the fascinating concept of sliders, particularly focusing on how to use them similarly to the popular Lora technique. With sliders, you can adjust various features of your generated images with...
An Introduction to BROS: Extracting Key Information from Documents
In this article, we will explore the BROS (BERT Relying On Spatiality) model, an innovative pre-trained language model designed to focus on both textual and spatial data for extracting key information from documents. We’ll dive into how you can utilize BROS for...
How to Effectively Utilize GGUF Files with SicariusSicariiStuffDusk_Rainbow
Diving into the world of AI model quantization can seem daunting at first, but with the right guidance, it becomes as easy as pie! In this article, we will explore the SicariusSicariiStuffDusk_Rainbow model and how to effectively use GGUF files. Whether you're a...
How to Effectively Use GGUF Files for AI Development
Welcome to the world of AI and quantization! In this guide, we'll explore how to utilize GGUF (Generalized Generalized Universal Format) files to make the most out of your AI models. Whether you are a seasoned developer or a novice, this user-friendly article will...
How to Access Pyannote’s Overlapped Speech Detection Model
If you've come across the Pyannote overlapped speech detection model and found that access is restricted, you're not alone. This model is designed to tackle the complex issue of detecting overlapping speech in audio recordings, but getting the necessary permissions to...